As you know, a video file consists of video streams (MJPEG, H.264, etc.) and audio streams (MP3, AAC, etc.), packed into one of the media containers (AVI, MP4, etc.).
There is a wide variety of standards and specifications. The standards and specifications themselves leave quite a lot of freedom for developers. This leads to the fact that most device models and video editors leave their traces in the files they create. This is very important for forensic video expertise, because it allows to determine the origin of the video file. On the Internet you can find publications on the subject, for example:
- Gloe, A. Fischer, and M. Kirchner, “Forensic analysis of video file formats,” Digital Investigation, 2014, Volume 11, no. Supplement 1, pp. 68–76, May 2014.
- R. Hall, “Mpeg-4 video authentication using file structure and metadata”. Masters of Science dissertation. University of Colorado, US - Colorado, 2015.
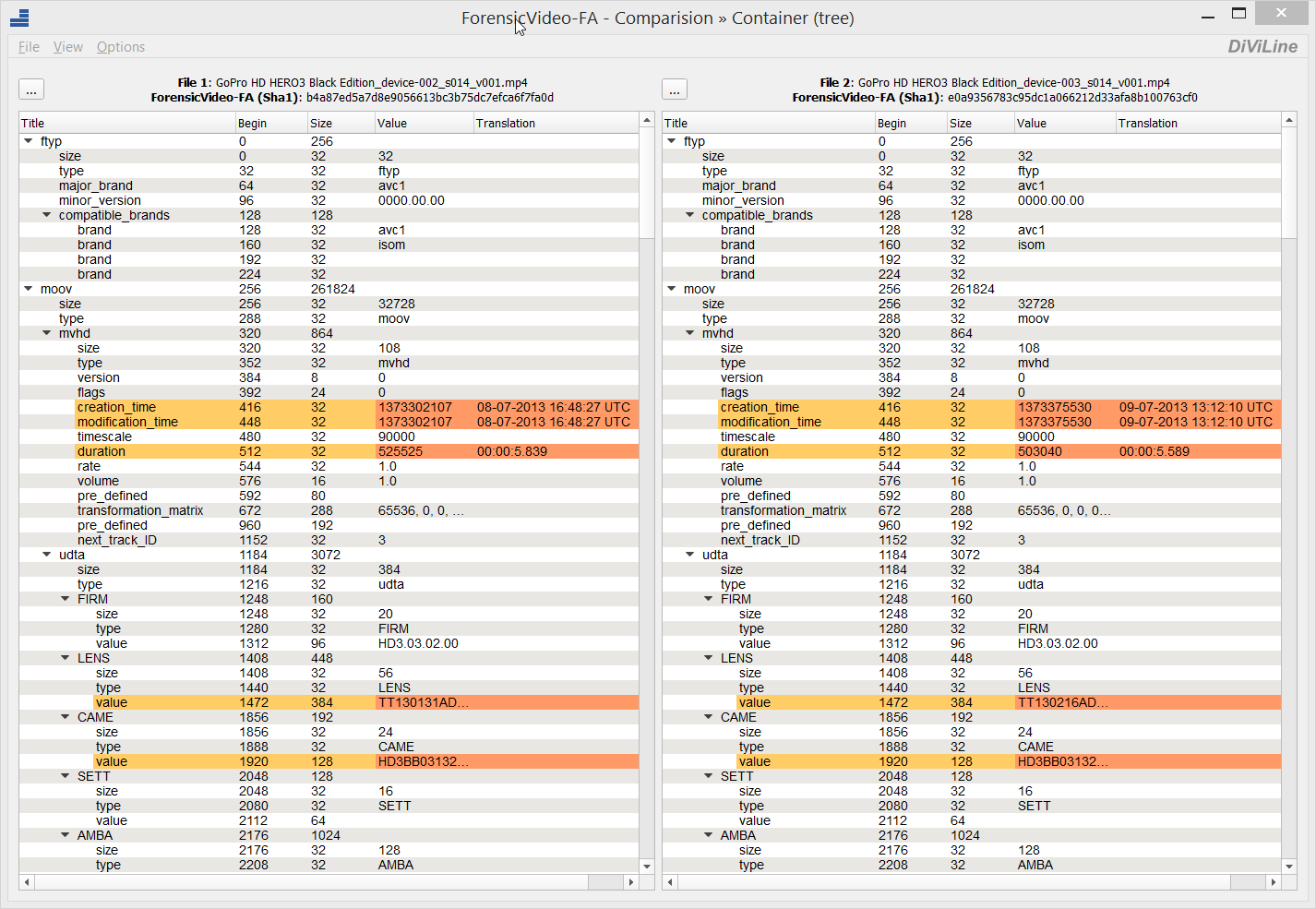
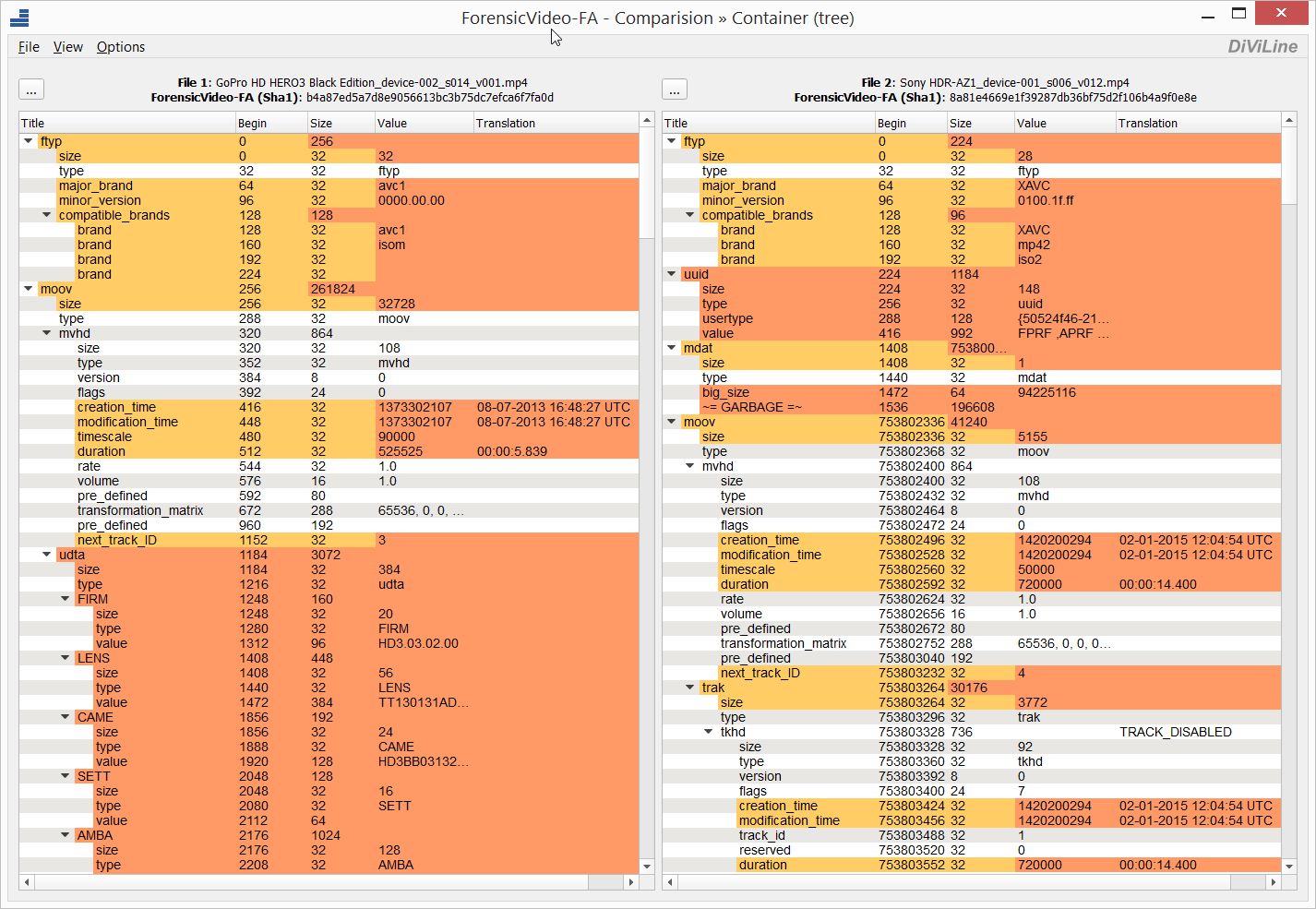
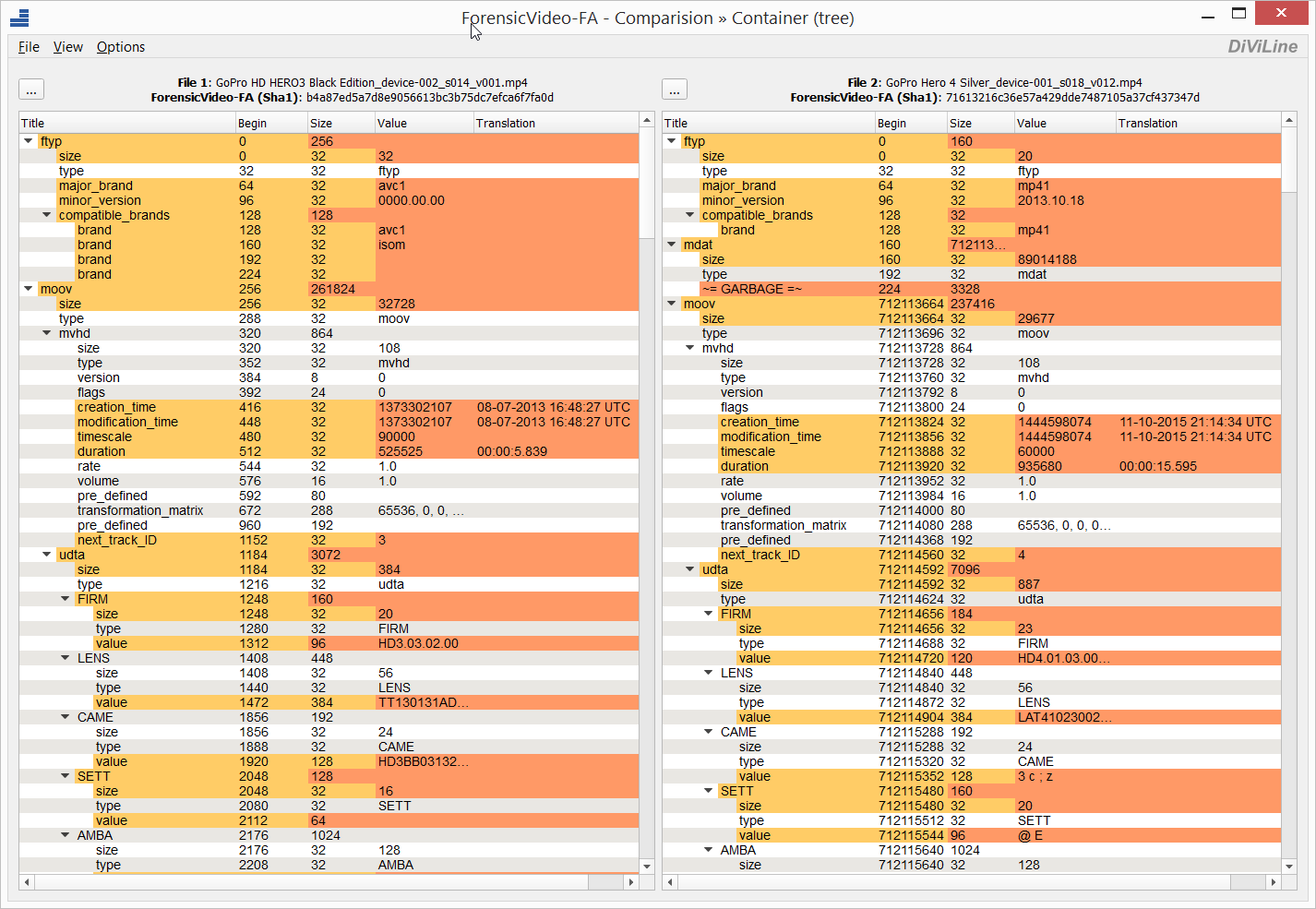
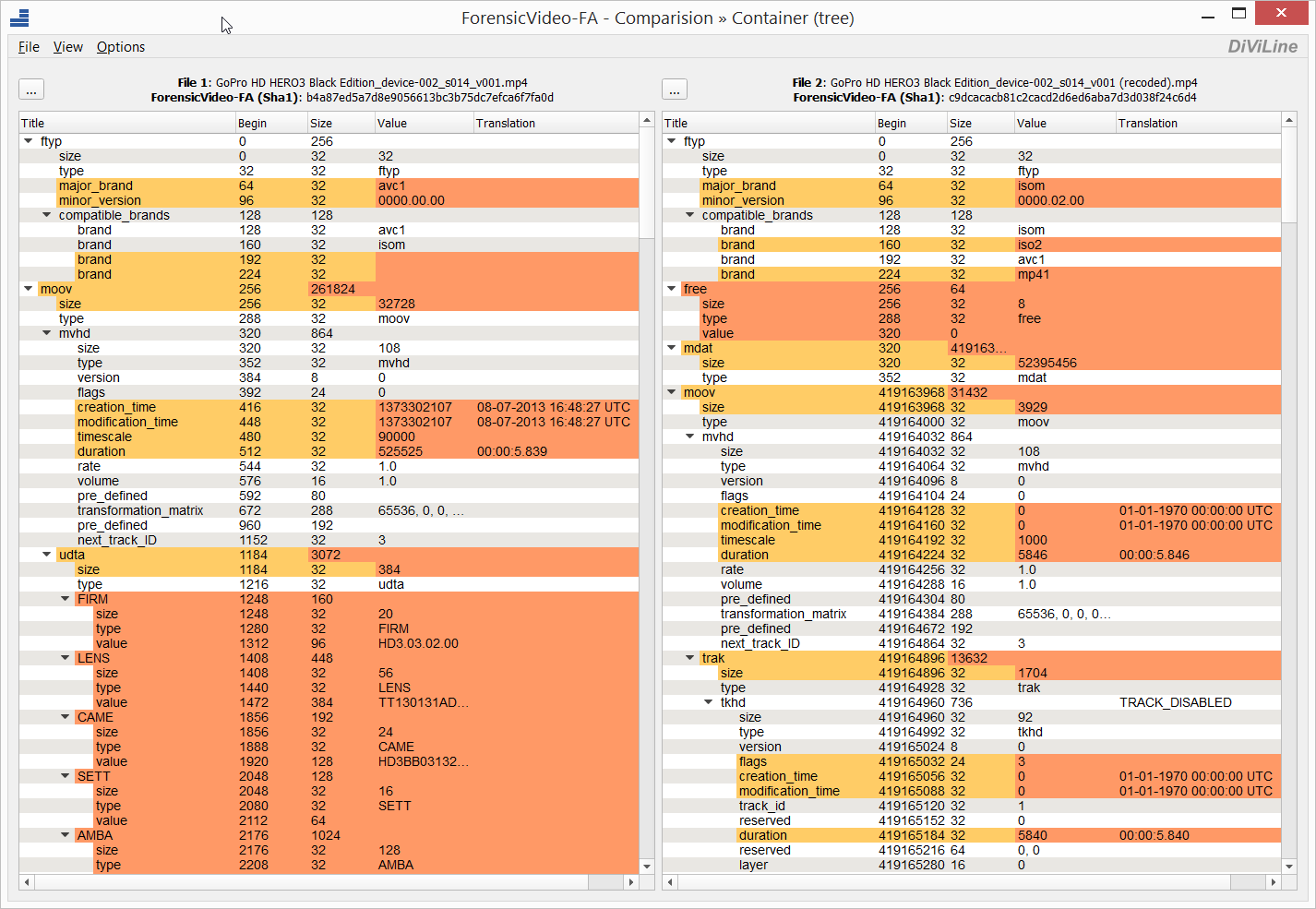
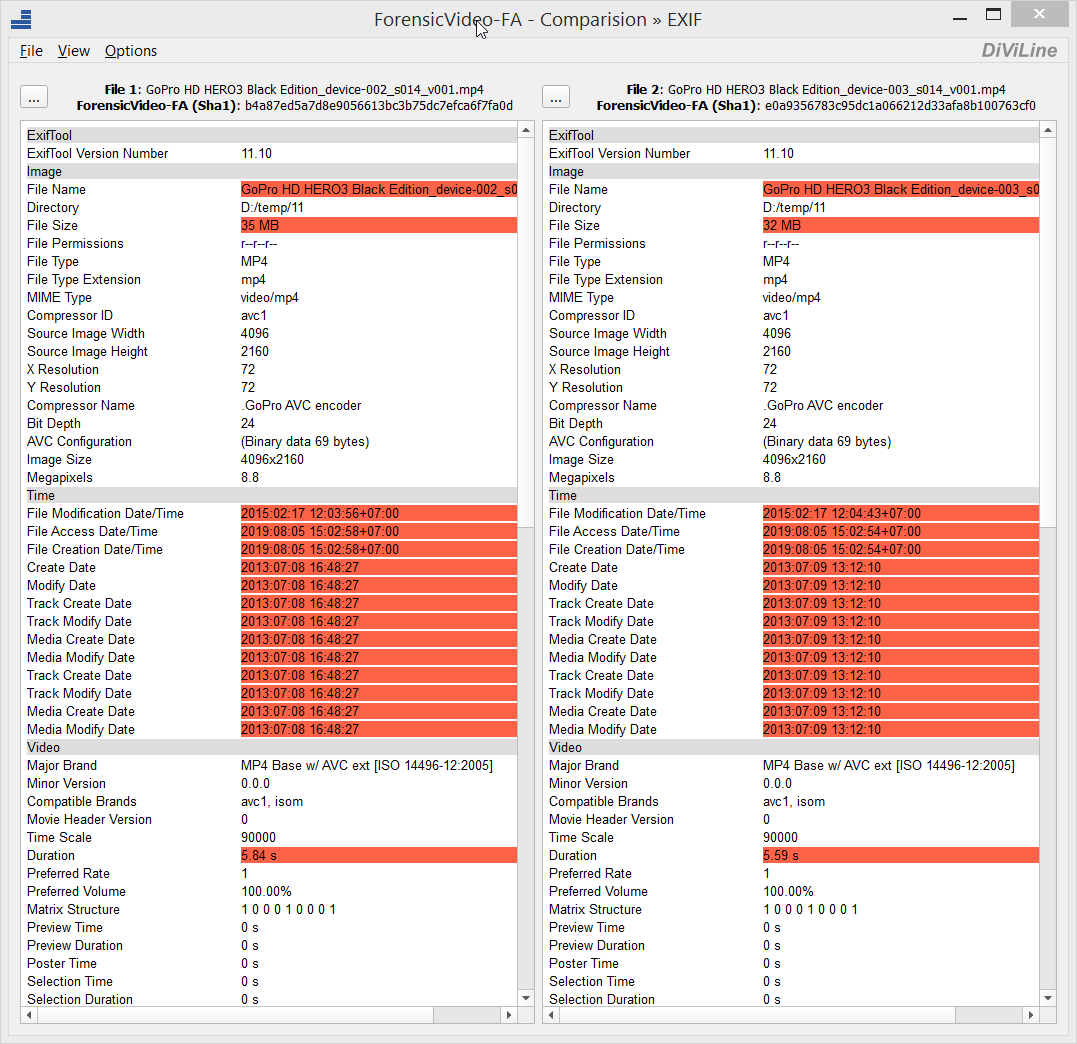
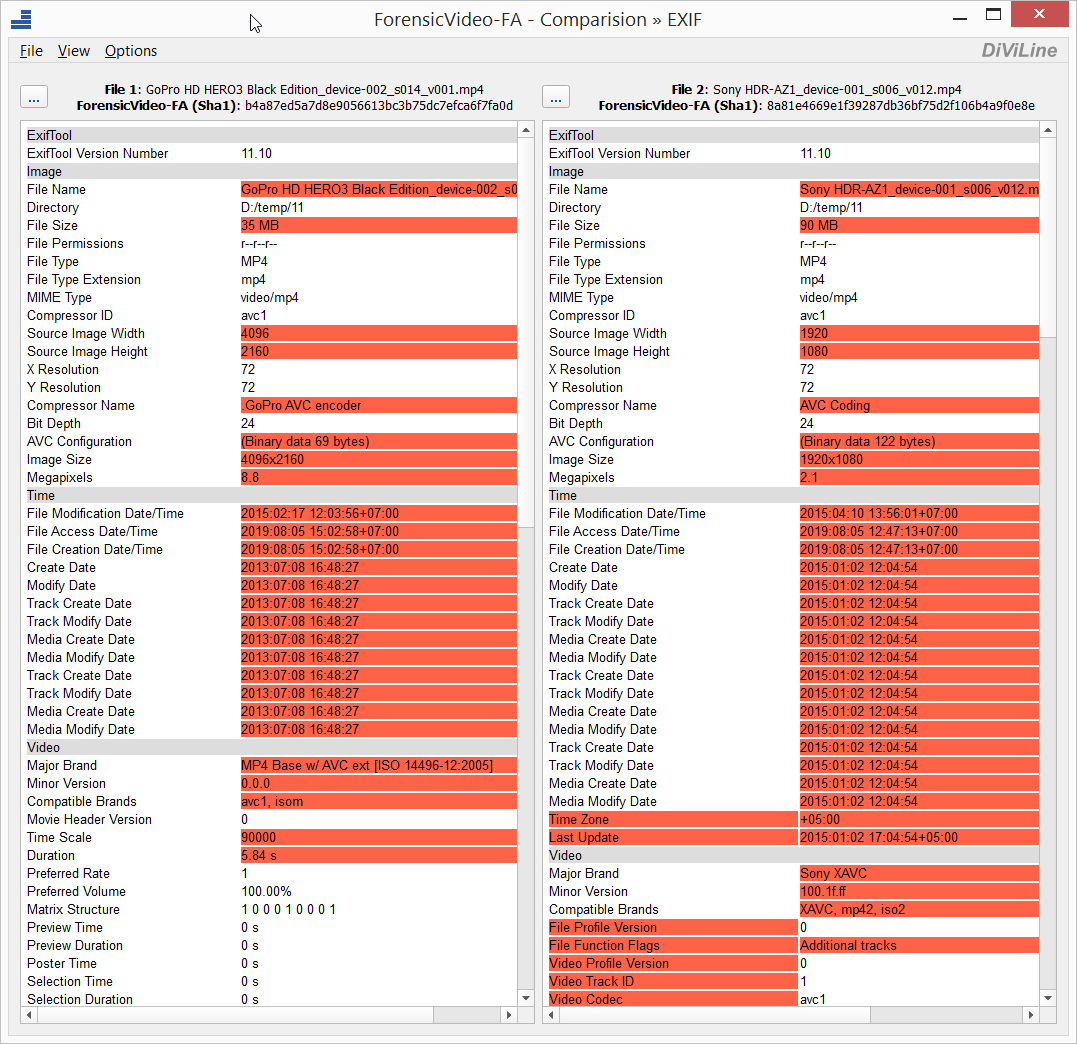
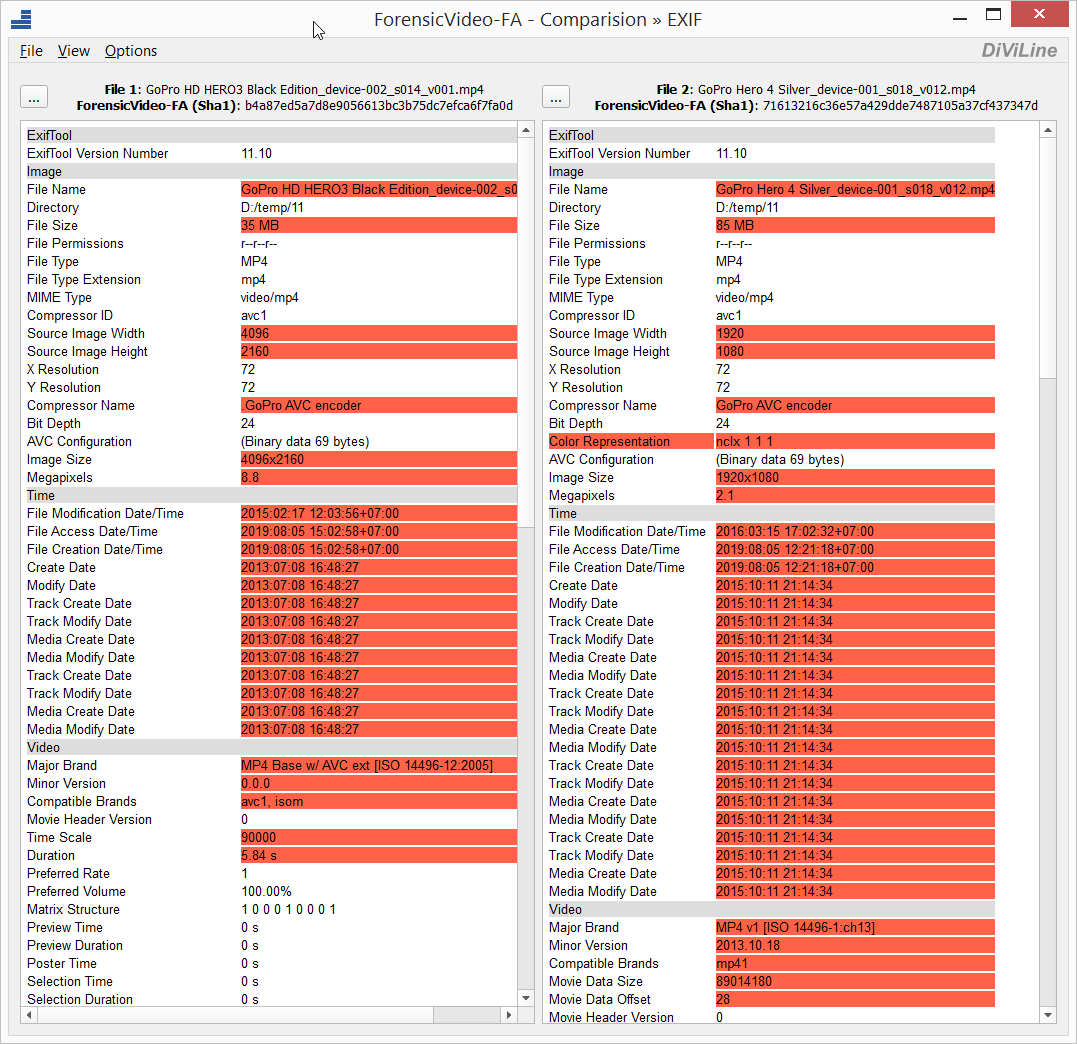
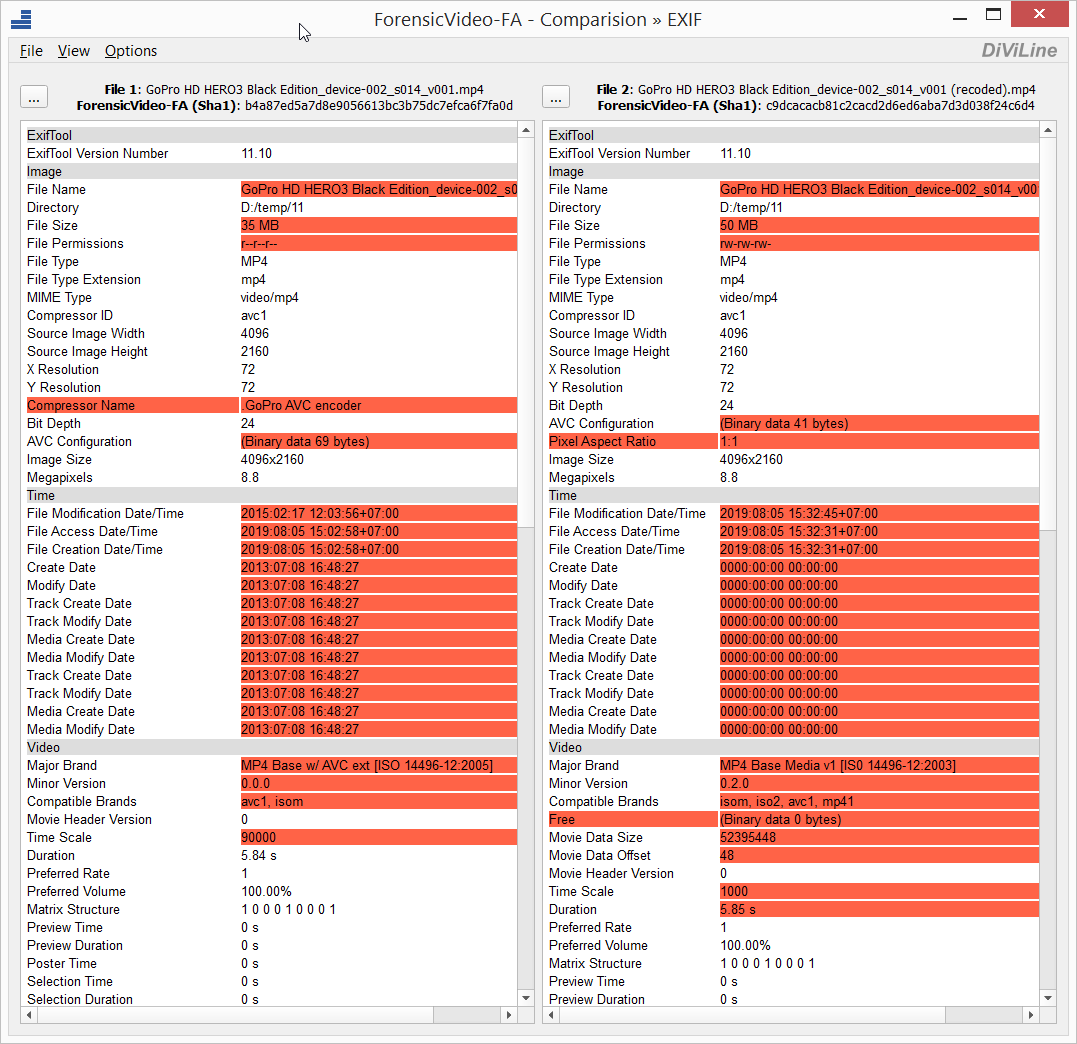
The software ForensicVideo-FA is designed to analyze the structure of video files. In addition to the possibility of in-depth analysis of video file parameters, ForensicVideo-FA includes a tool for comparing video file structures. With the use of ForensicVideo-FA for video files can be compared:
- media container elements (trees);
- video stream elements (trees);
- summary information about video files;
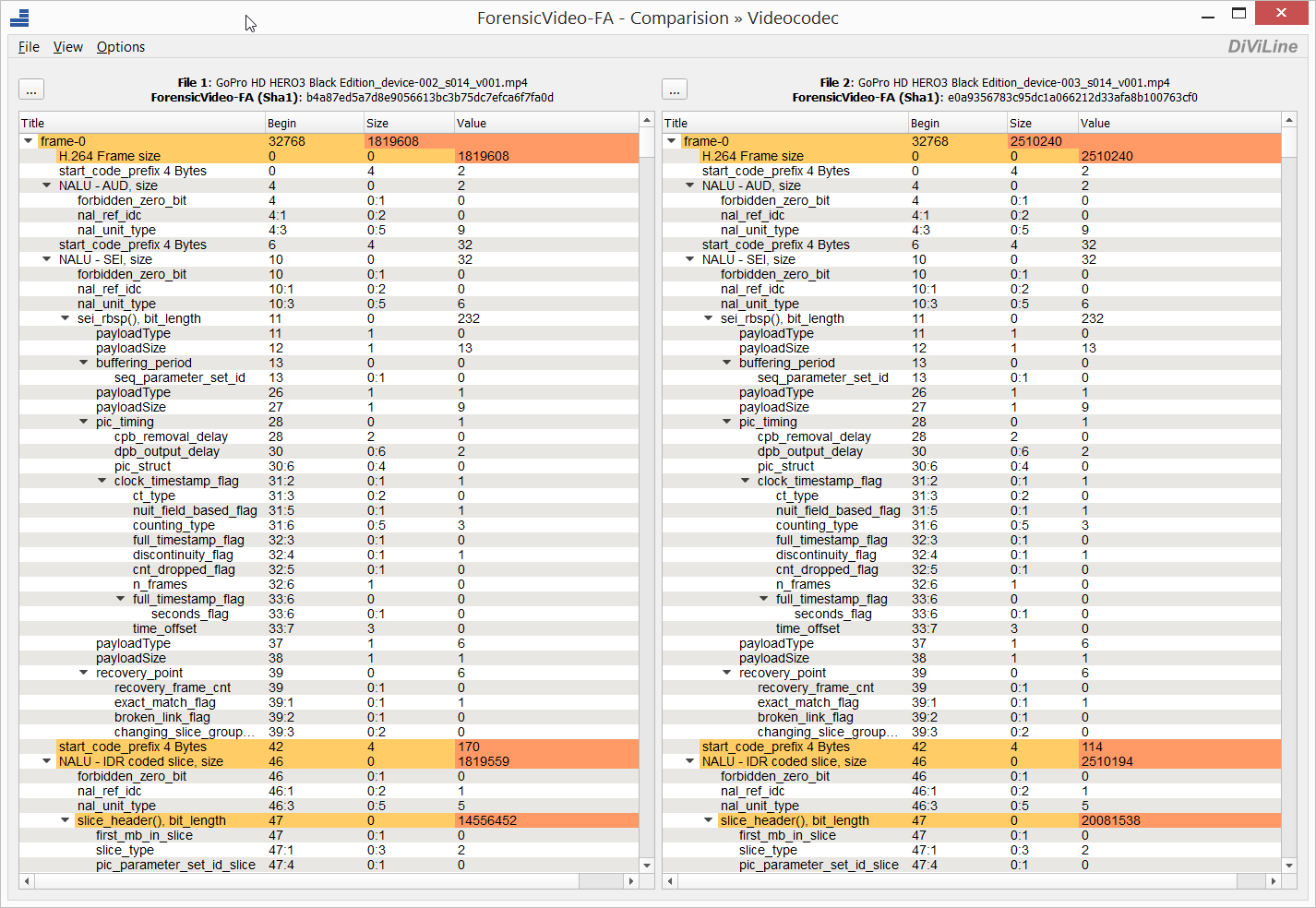
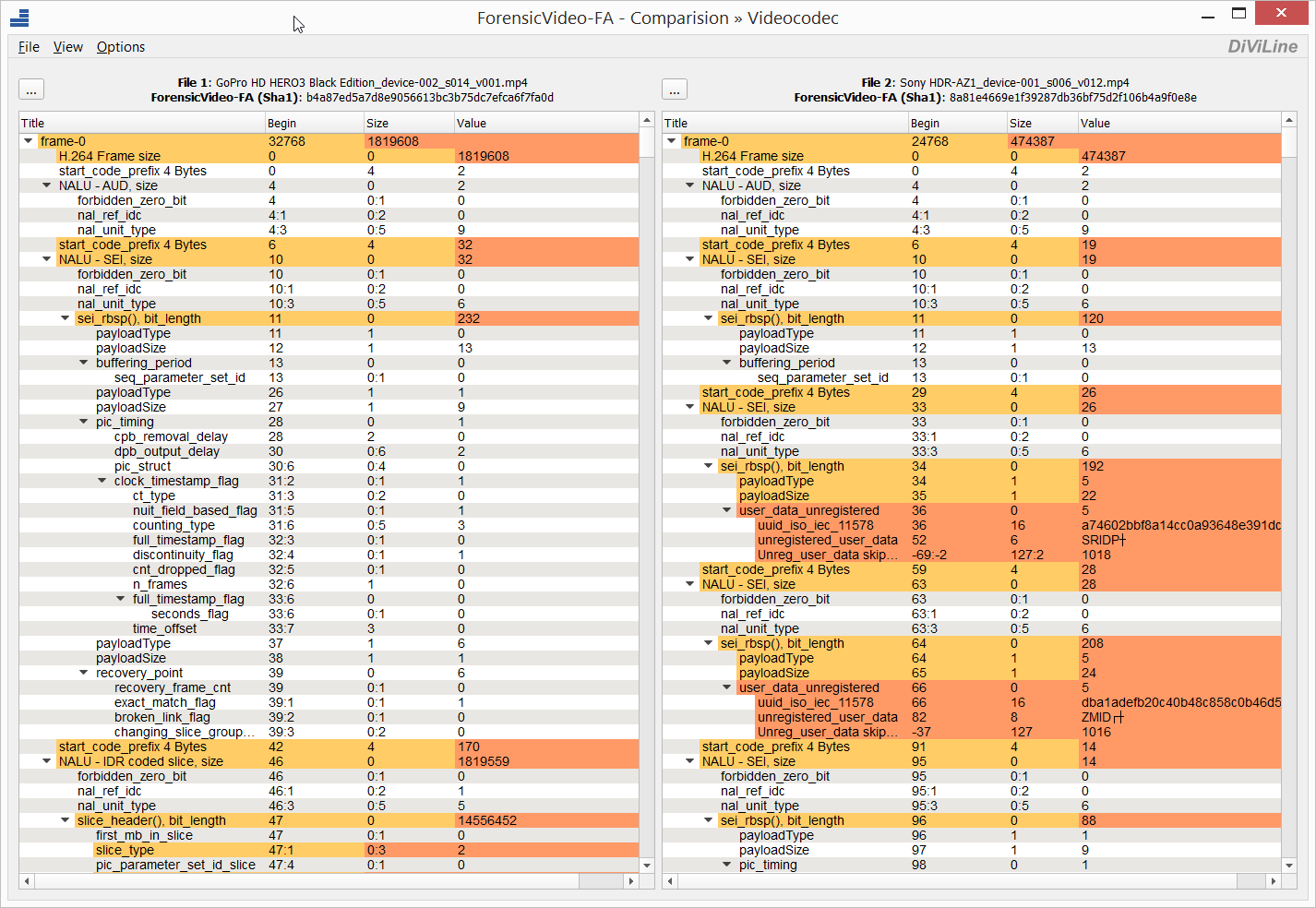
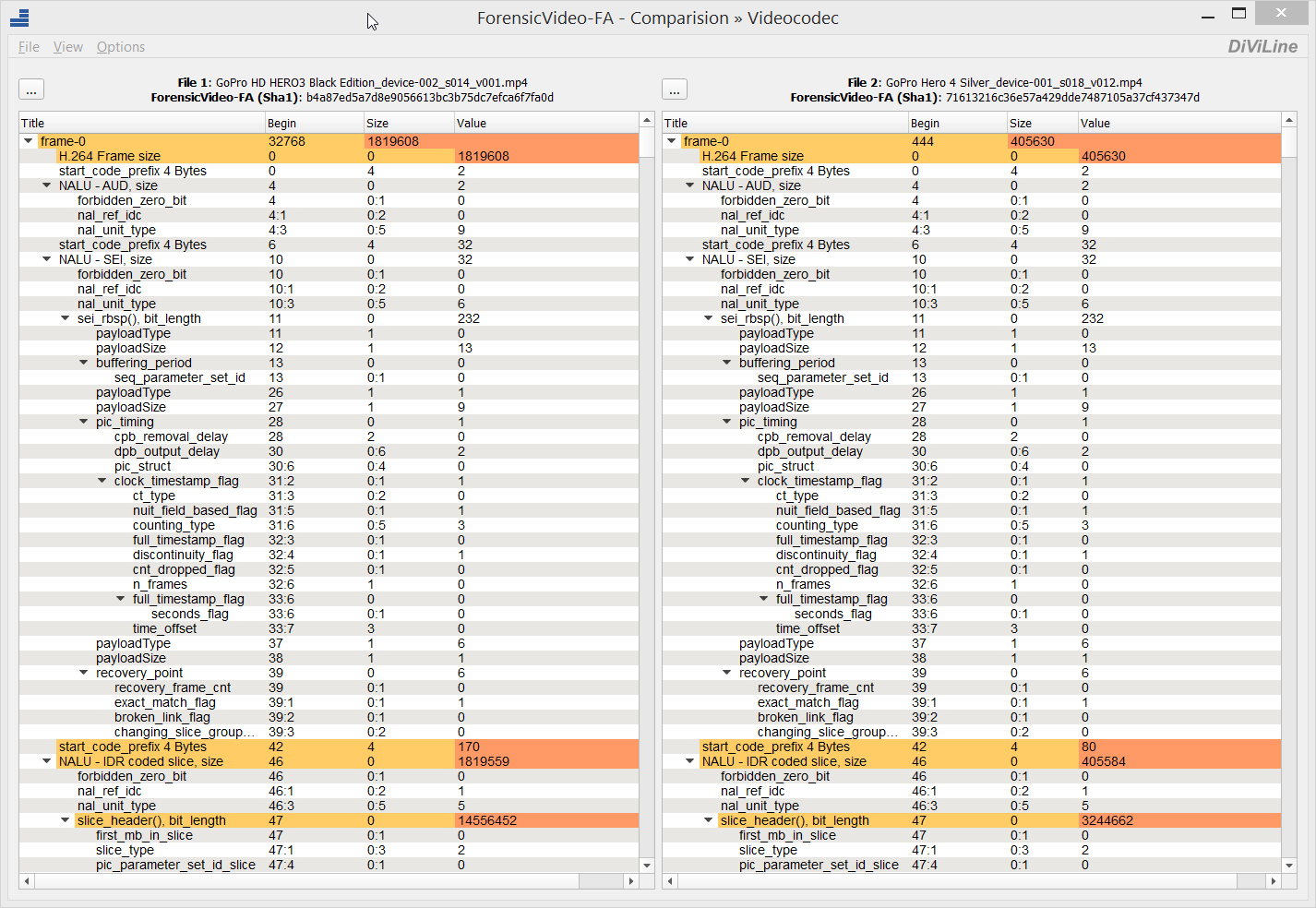
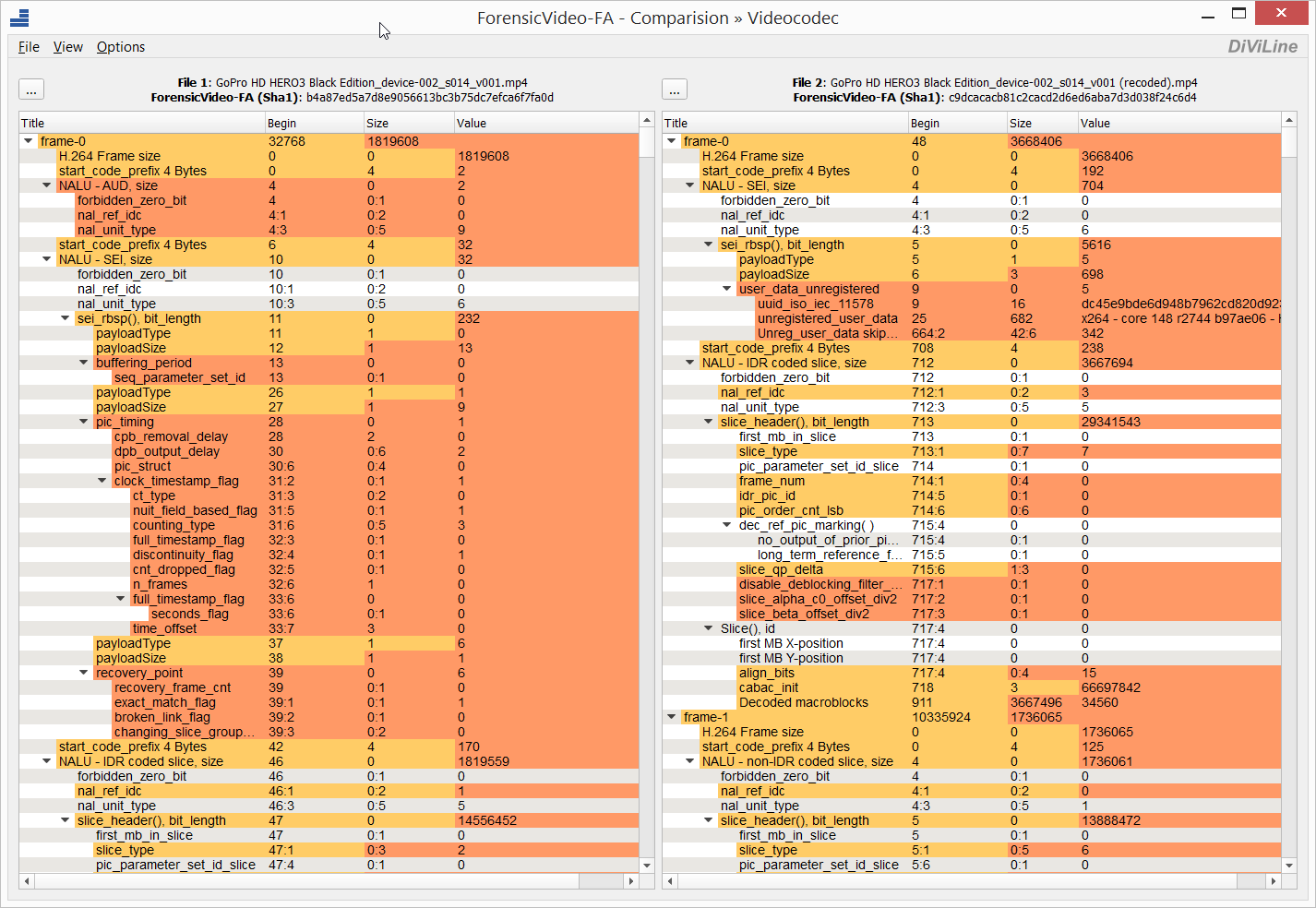
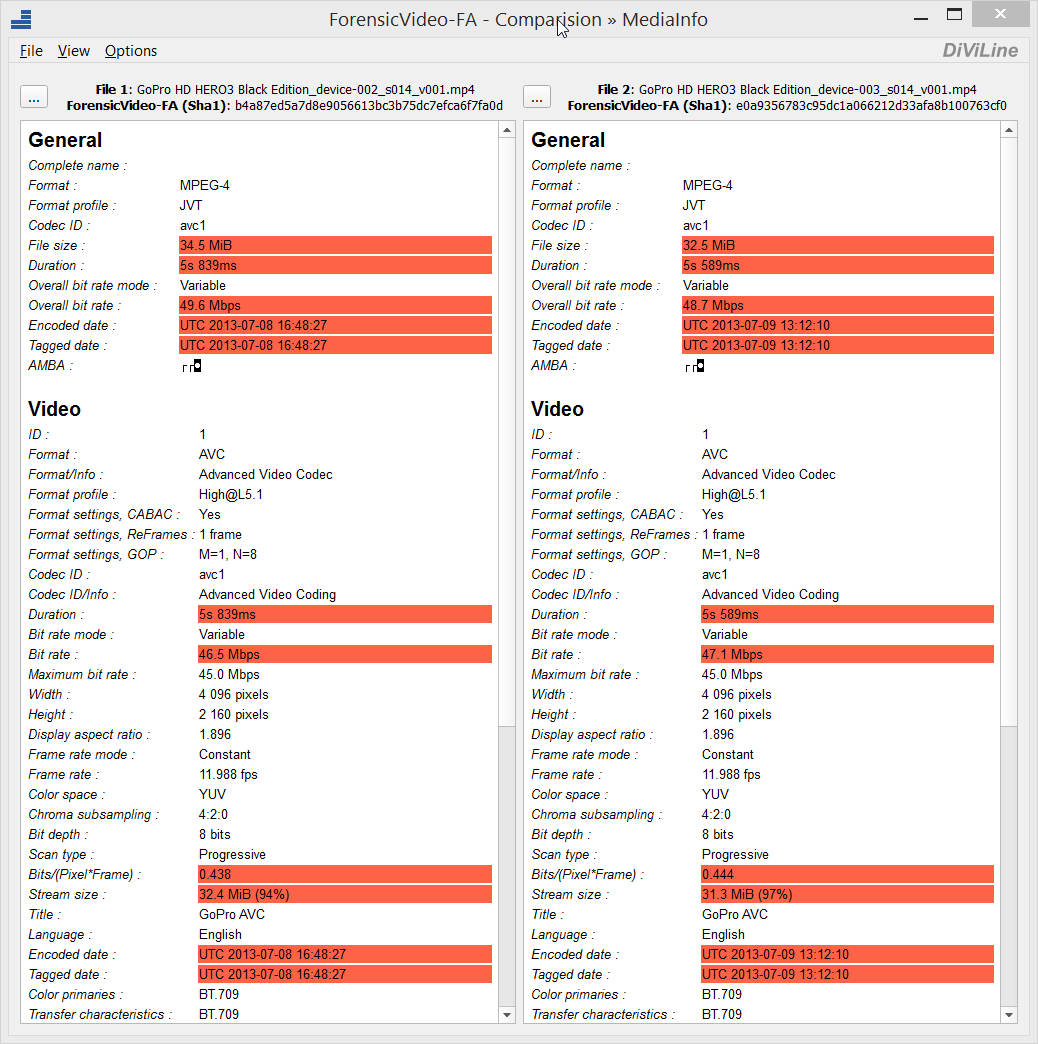
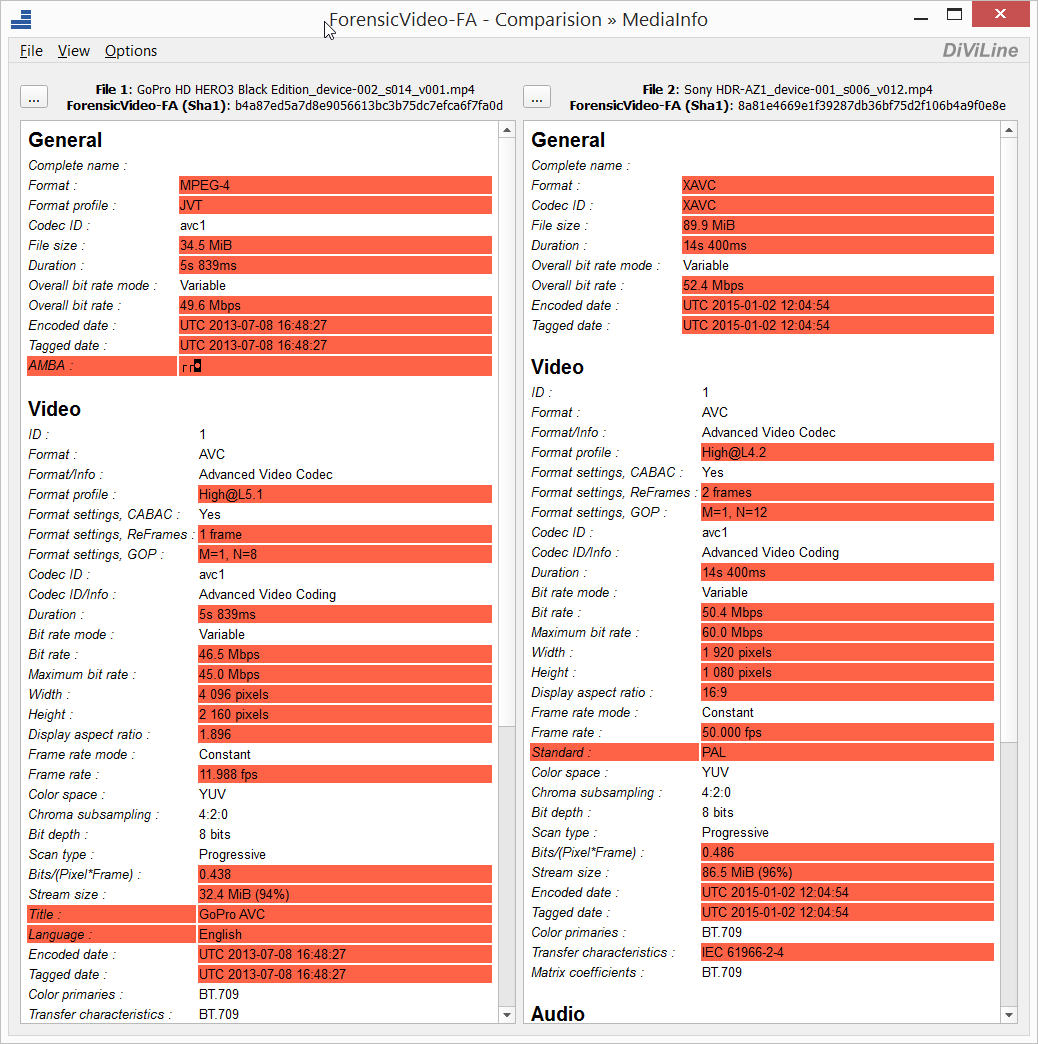
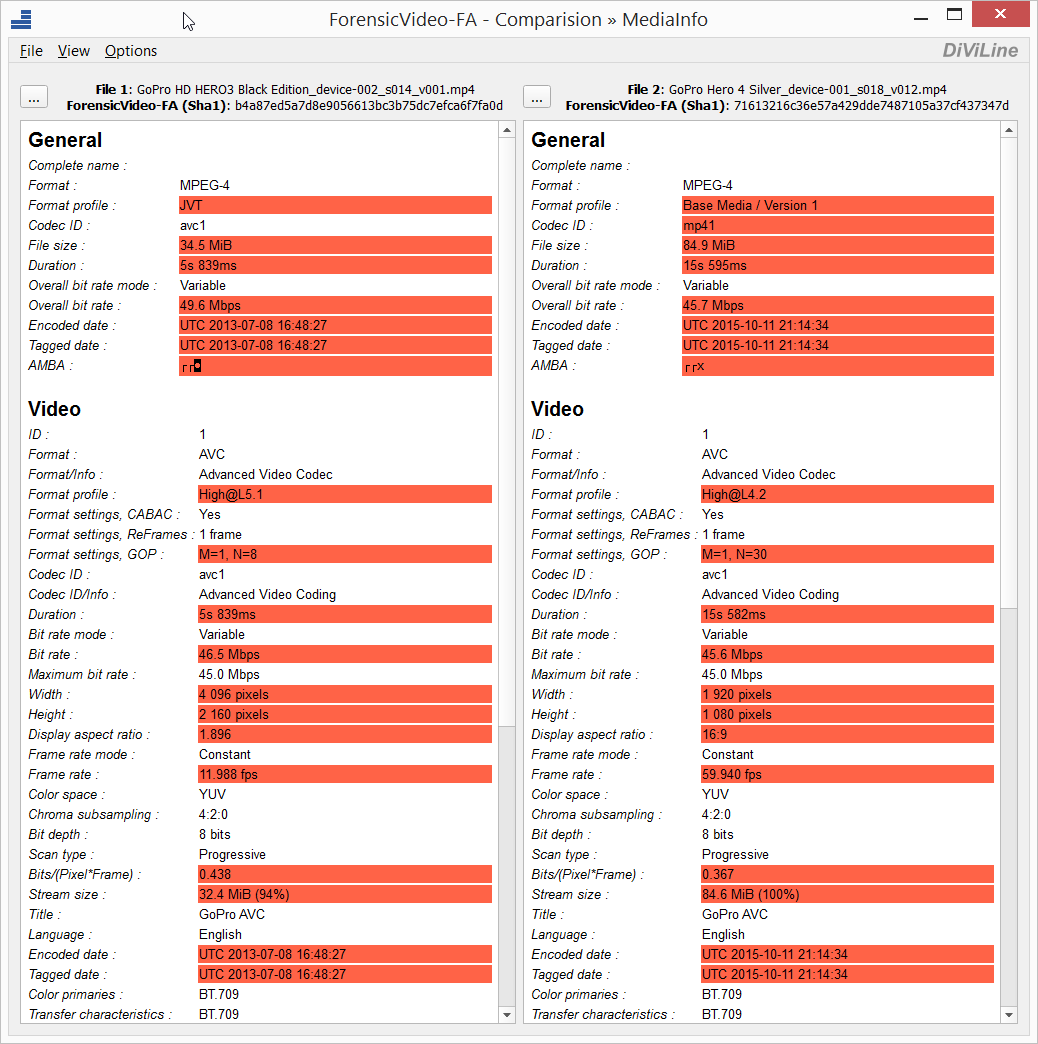
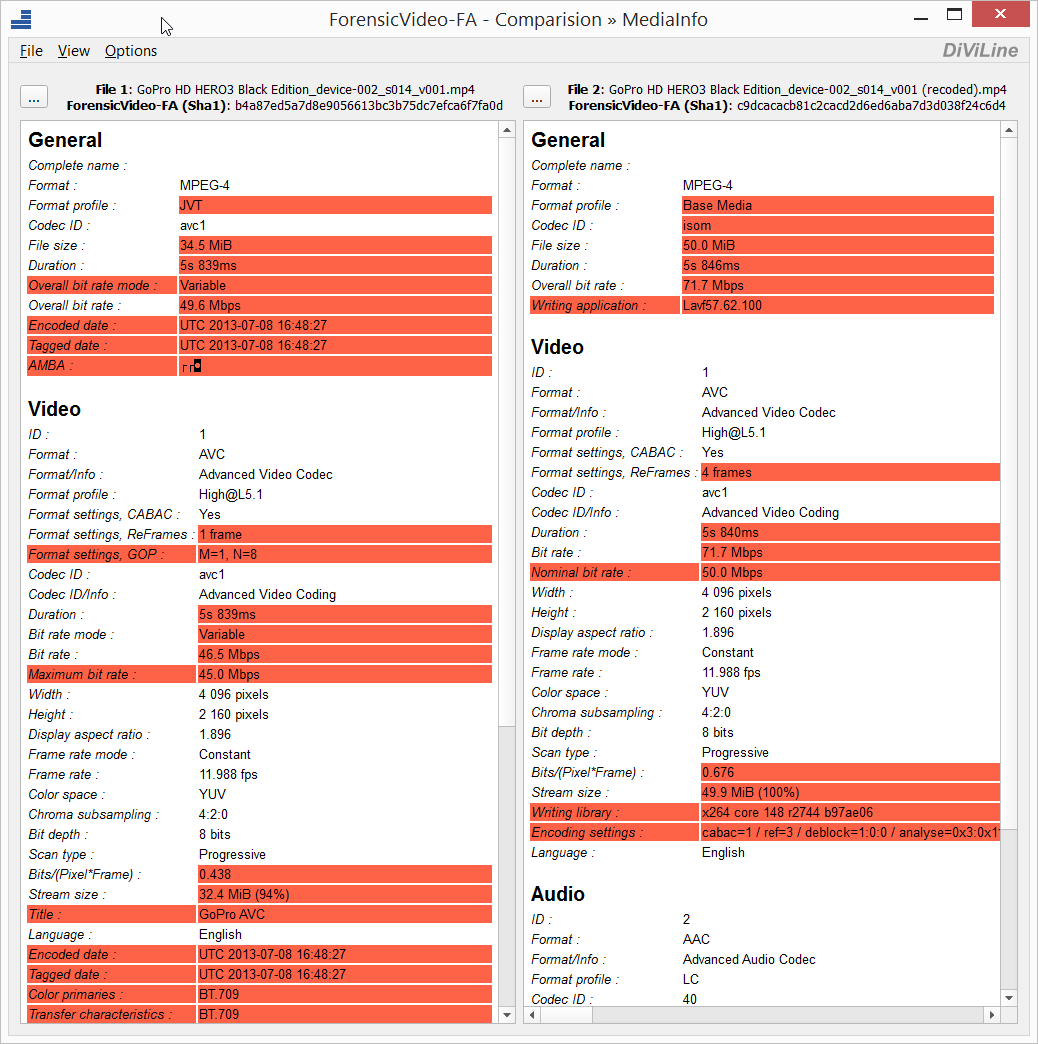
The emergence of such a tool will allow experts to identify signs of recompression of video files and determine the identity of the origin of two or more video files.
The following are examples of video file format comparisons using ForensicVideo-FA.
Forensicvideo-FA - MP4 video files structure comparision (different device models)
Forensicvideo-FA - MP4 video files structure comparision (two devices of the same model)
ForensicVideo-FA video examples of comparision/analysis for .mp4 video files.
Fig. 1 - ForensicVideo-FA comparision/analysis of media conteiners for .mp4 video files.
Fig. 2 - ForensicVideo-FA comparision/analysis of h.264 video streams for .mp4 video files.
Fig. 3 - ForensicVideo-FA comparision/analysis of MediaInfo data for .mp4 video files.
Fig. 4 - ForensicVideo-FA comparision/analysis of ExifTool data for .mp4 video files.